Deploy Open Banking APIs
This page explains how to deploy an Open Banking API.
Before publishing the APIs, need to create the consumer role in WSO2 API Manager.
Create Consumer Role APIM Console¶
-
Goto APIM Carbon Console:
https://<APIM_HOSTNAME>:9443/carbon -
Log into APIM Carbon Console using APIM admin username and password.
-
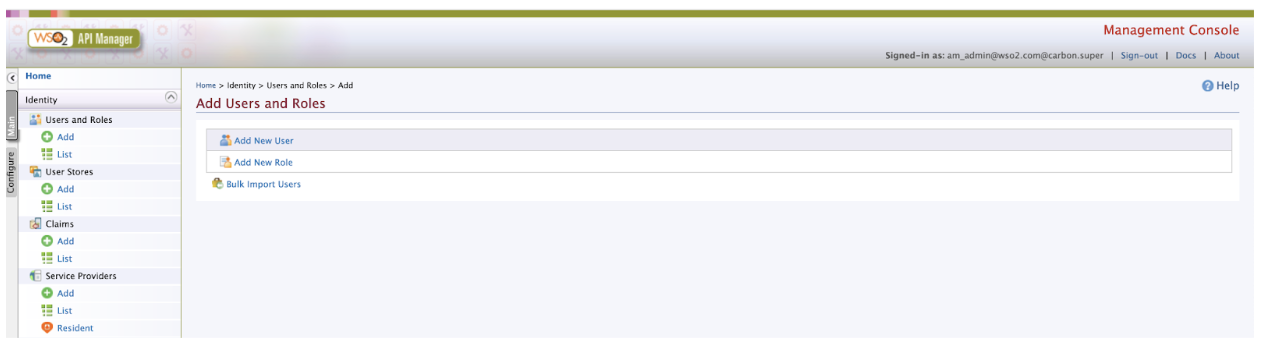
Click on Main Tab → Users and Roles → Add
-
Click on Add New Role.
-
Enter role Details:
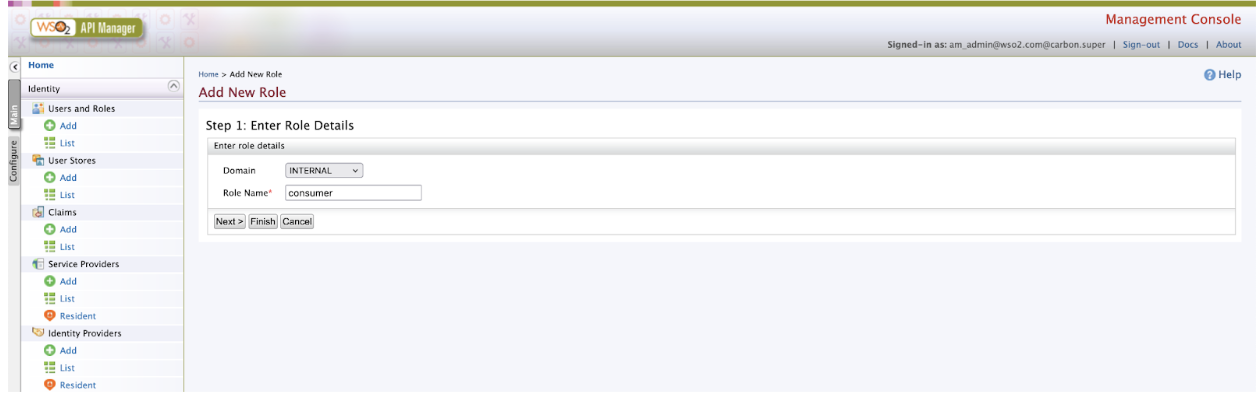
Domain Role Name INTERNAL consumer -
Click on Finish.
Tip
Download the sample Banking backend, extract the zip file and place the api#fs#backend.war inside <APIM_HOME>/repository/deployment/server/webapps folder.
Publish Open Banking APIs¶
Note
WSO2 Open Banking Accelerator supports Accounts flow, Payments flow and Confirmation of Funds flow. Publish all three APIs before trying out the flows.
-
Sign in to the API Publisher Portal at
https://<APIM_HOSTNAME>:9443/publisher. -
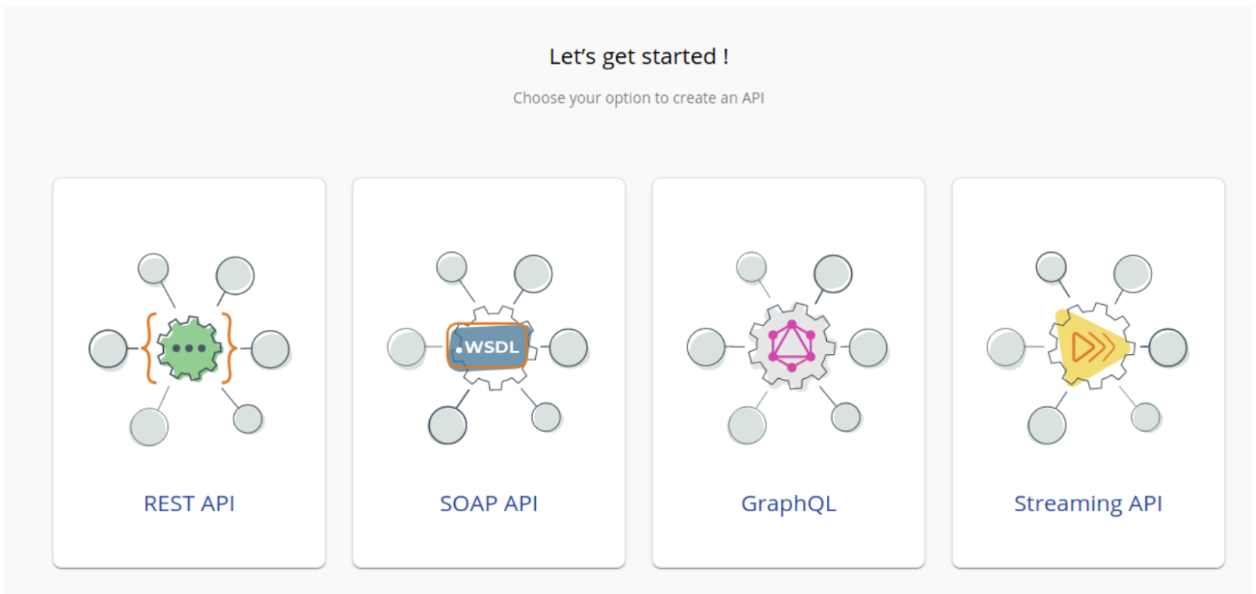
In the homepage, go to REST API and select Import Open API.
-
Select OpenAPI File/Archive.
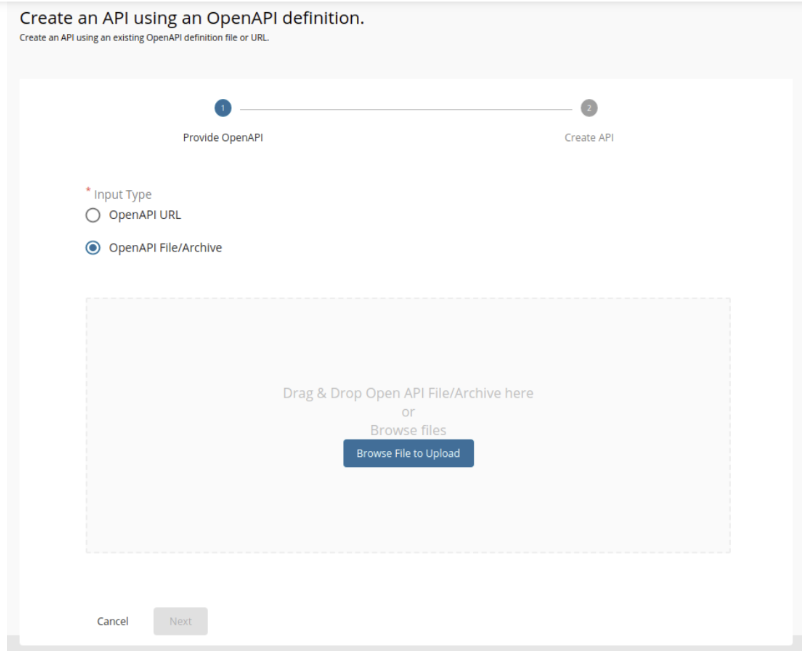
-
Click Browse File to Upload and select the required yaml file.
API Swagger File Accounts account-info-swagger.yaml Payments payment-initiation-openapi.yaml Confimation of Funds funds-confirmation-openapi.yaml -
Click Next.
-
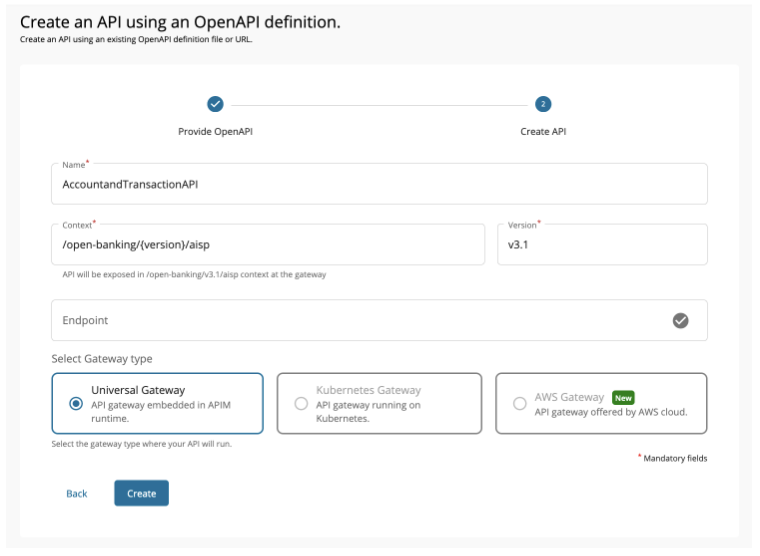
Set the Context value as follows:
API Context Value Accounts /open-banking/{version}/aispPayments /open-banking/{version}/pispConfimation of Funds /open-banking/{version}/cbpii -
Leave the Endpoint field empty as it is, Select the Gateway Type and click Create.
-
Select Subscriptions from the left menu pane and uncheck all subscription plans.
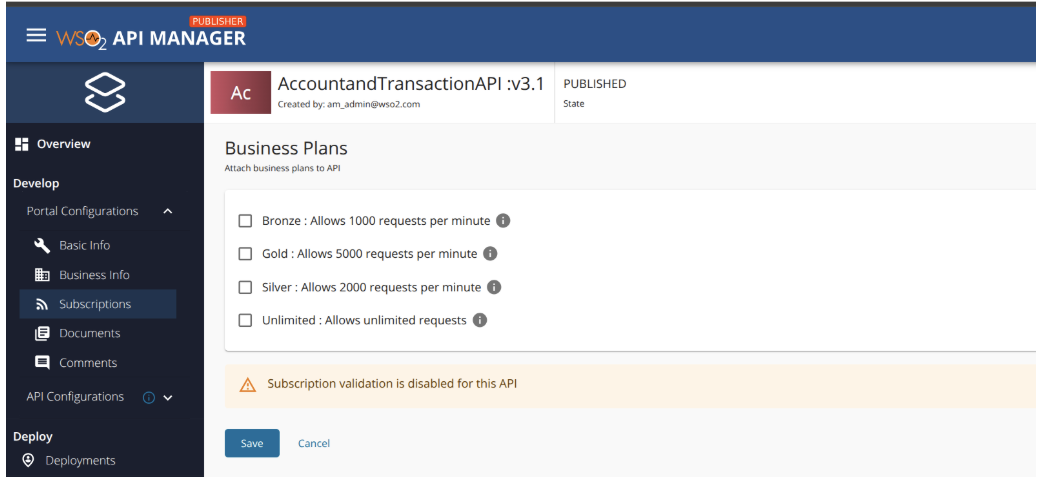
-
Click Save.
-
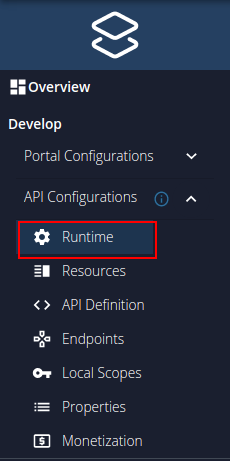
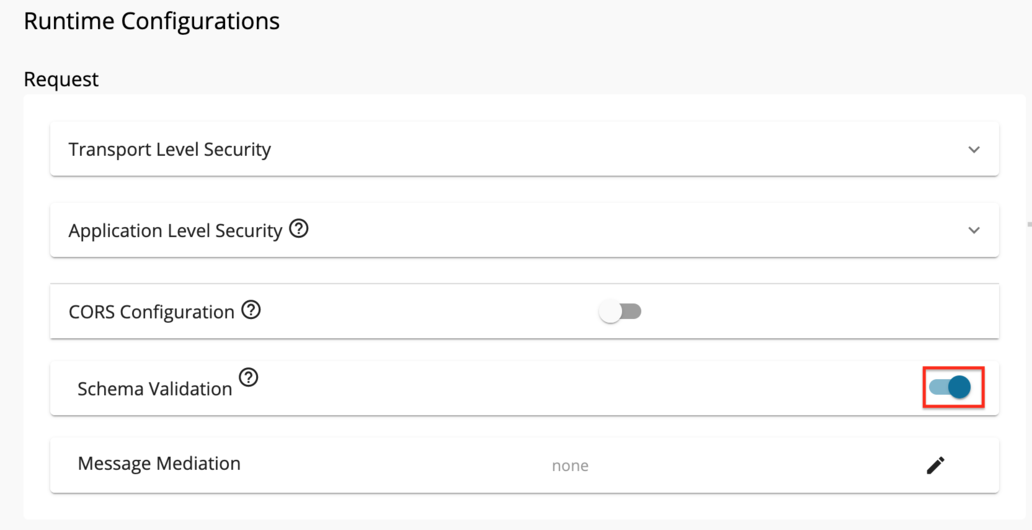
Go to Runtime using the left menu pane.
-
Toggle the Schema Validation button to enable Schema Validation for all APIs except for the Dynamic Client Registration API.
-
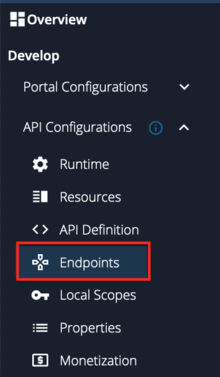
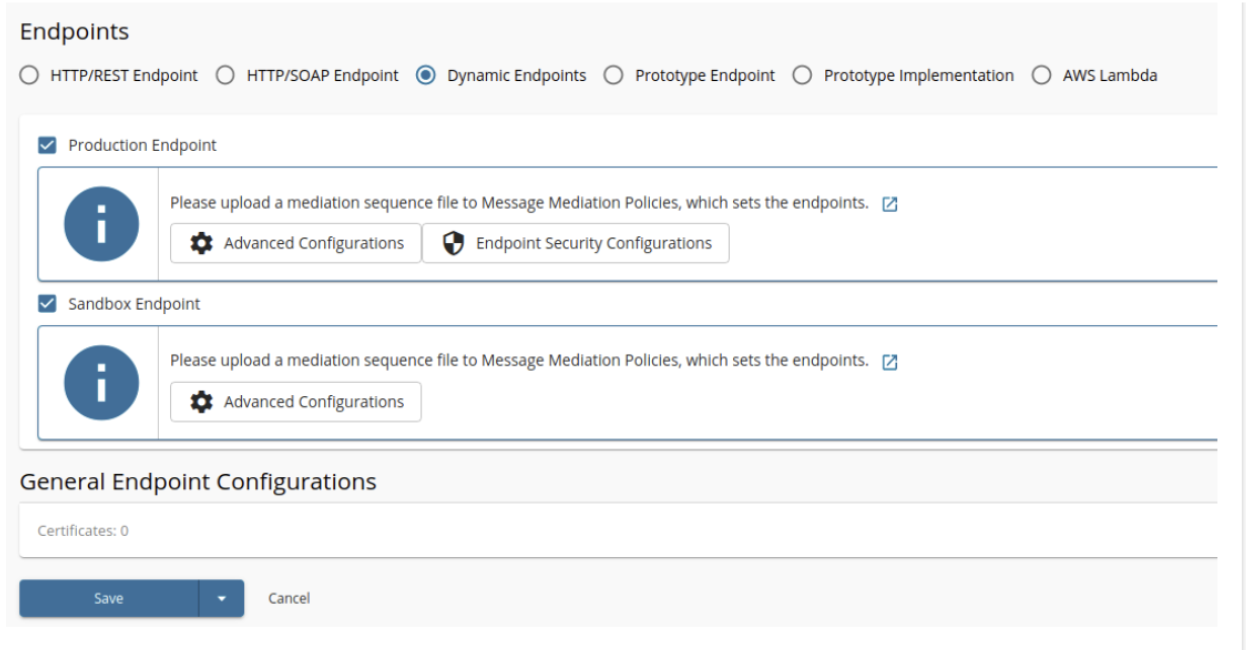
Go to Endpoints using the left menu pane.
-
Select the endpoint types; Dynamic Endpoints and click Save.
-
Add JWT claim based access validation as an Operational Policy.
Use aut as the Access verification claim name and value from below.
Token Type Claim Value Client Credentials Grant APPLICATION Authorization Code Grant APPLICATION_USER -
Create and engage the required Inbuilt Gateway Enforcements
- Refer the Introduction to Policies for more details on Policies.
- Refer the Create Policies for create new Policies.
- Refer the Engage Policies to learn how to engage policies to an API.
Refer to the below table and engage the required policies for each API.
API API Level Policies Operational Level Policies Accounts MTLS Enforcement PolicyConsent Enforcement PolicyDynamic Endpoint PolicyPayments MTLS Enforcement PolicyConsent Enforcement PolicyDynamic Endpoint PolicyConfirmation of Funds MTLS Enforcement PolicyConsent Enforcement PolicyDynamic Endpoint Policy -
Select the API Gateway type, in this scenario, it is Default.
-
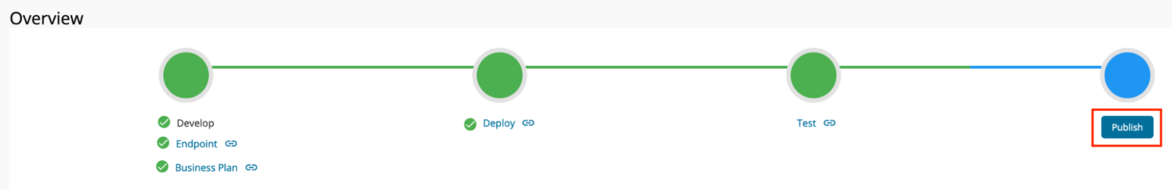
Click Deploy.
-
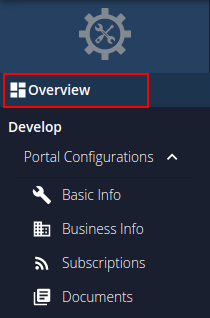
Go to Overview using the left menu pane.
-
click Publish.
Once you deploy the APIs an API resource will be created along with the role mentioned in the swagger on the Identity Server side.
Note
If you have created the users, assign the roles created while publishing the APIs to the users.