Using Manual Client Registration Flow
This page explains how to onboard API consumers using the Manual Client Registration.
Before you begin:
See the Configurations section and configure Manual Client Registration.
Configure FS Key Manager in WSO2 API Manager¶
-
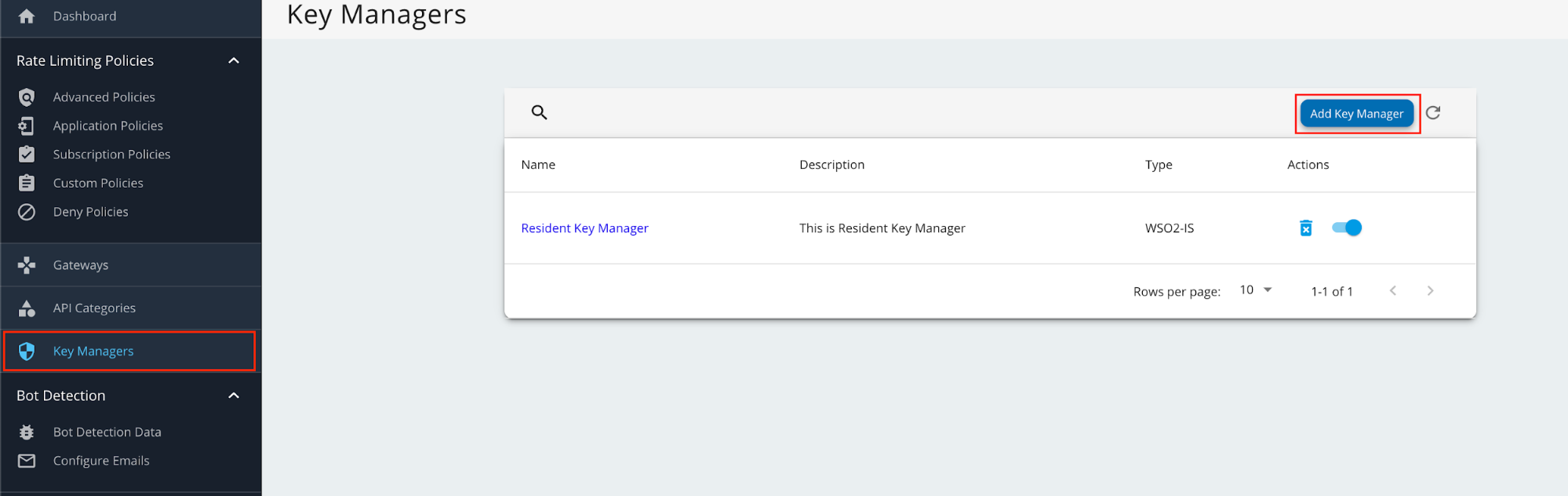
Sign in to the Admin Portal of API Manager at
https://<APIM_HOSTNAME>:9443/adminusing admin credentials. -
Go to Key Managers on the left main menu. Click on Add Key Manager button.
-
Enter a Name and Display Name, and select fsKeyManager as the Key Manager Type.
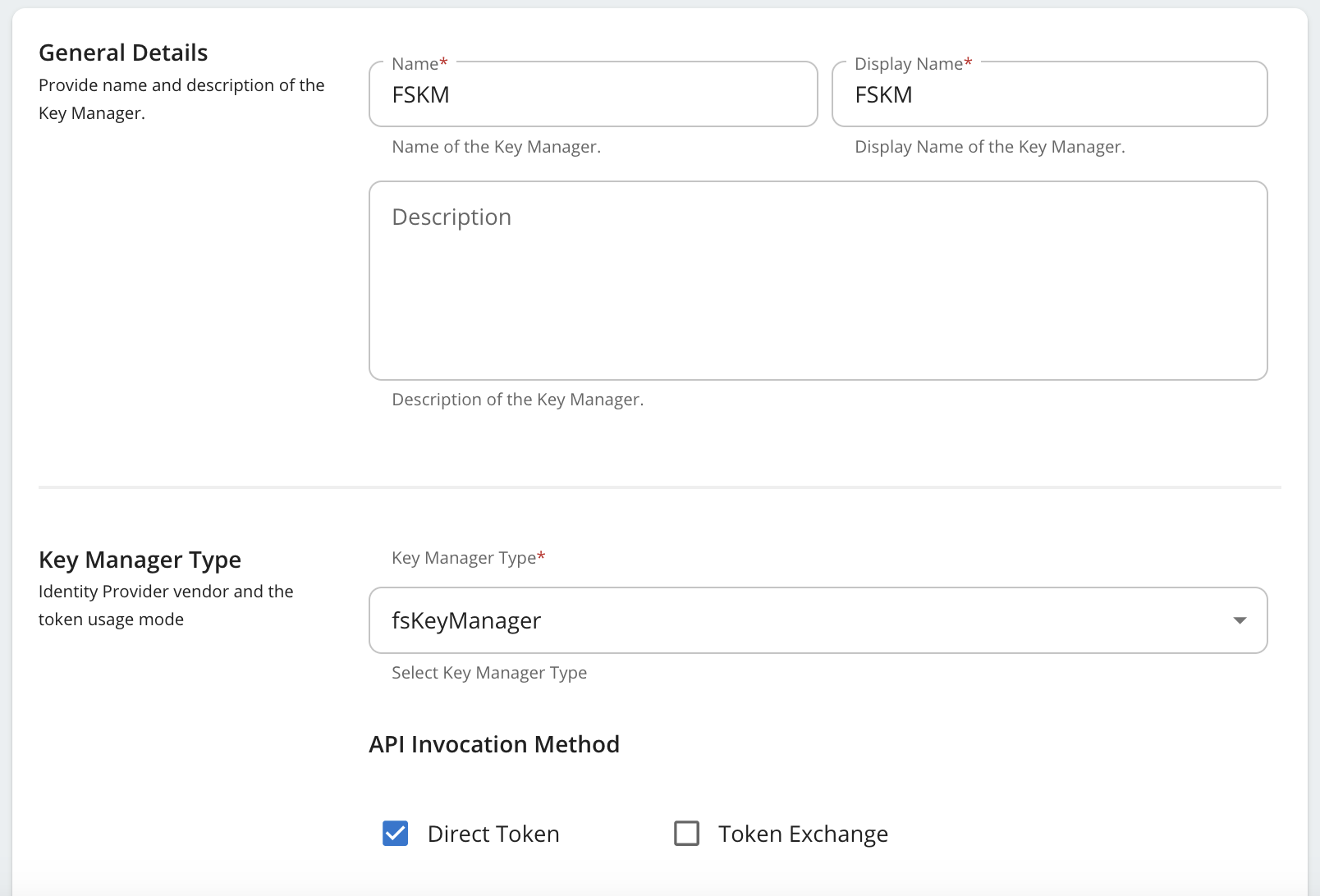
-
Enter the Well-known-url and Issuer as below.
Field Value Well-known-url https://<IS_HOSTNAME>:9446/oauth2/token/.well-known/openid-configurationIssuer https://<IS_HOSTNAME>:9446/oauth2/token -
Under the Key Manager Endpoints section, provide the following values:
Note
You can use
https://<IS_HOSTNAME>:9446/oauth2/token/.well-known/openid-configurationas the Well-known URL, and click on Import to populate most of the fields mentioned below, Grant types, and the Certificates section.If the Import button is used, verify all the auto imported values with the onces mentioned below.
Configuration Values Issuer https://<IS_HOSTNAME>:9446/oauth2/tokenClient Registration Endpoint https://<IS_HOSTNAME>:9446/api/identity/oauth2/dcr/v1.1/registerIntrospection Endpoint https://<IS_HOSTNAME>:9446/oauth2/introspectToken Endpoint https://<IS_HOSTNAME>:9446/oauth2/tokenDisplay Token Endpoint https://<IS_HOSTNAME>:9446/oauth2/tokenRevoke Endpoint https://<IS_HOSTNAME>:9446/oauth2/revokeDisplay Revoke Endpoint https://<IS_HOSTNAME>:9446/oauth2/revokeUserInfo Endpoint https://<IS_HOSTNAME>:9446/scim2/MeAuthorize Endpoint https://<IS_HOSTNAME>:9446/oauth2/authorizeScope Management Endpoint https://<IS_HOSTNAME>:9446/api/identity/oauth2/v1.0/scopes -
Under Grant types, provide all the following:
- Client_credentials
- Refresh_token
- Authorization_code
- urn:ietf:params:oauth:grant-type:jwt-bearer
-
Under the Certificates section, select JWKS. Enter
https://<IS_HOSTNAME>:9446/oauth2/jwksas the URL. -
Under Connector Configurations, provide the following values:
Configuration Values Username Authorization server admin username Password Authorization server admin password WSO2 Identity Server 7 API Resource Management Endpoint https://<IS_HOSTNAME>:9446/api/server/v1/api-resourcesWSO2 Identity Server 7 Roles Endpoint https://<IS_HOSTNAME>:9446/scim2/v2/Roles -
Enable the Role creation is WSO2 Identity Server 7 as by ticking as below.
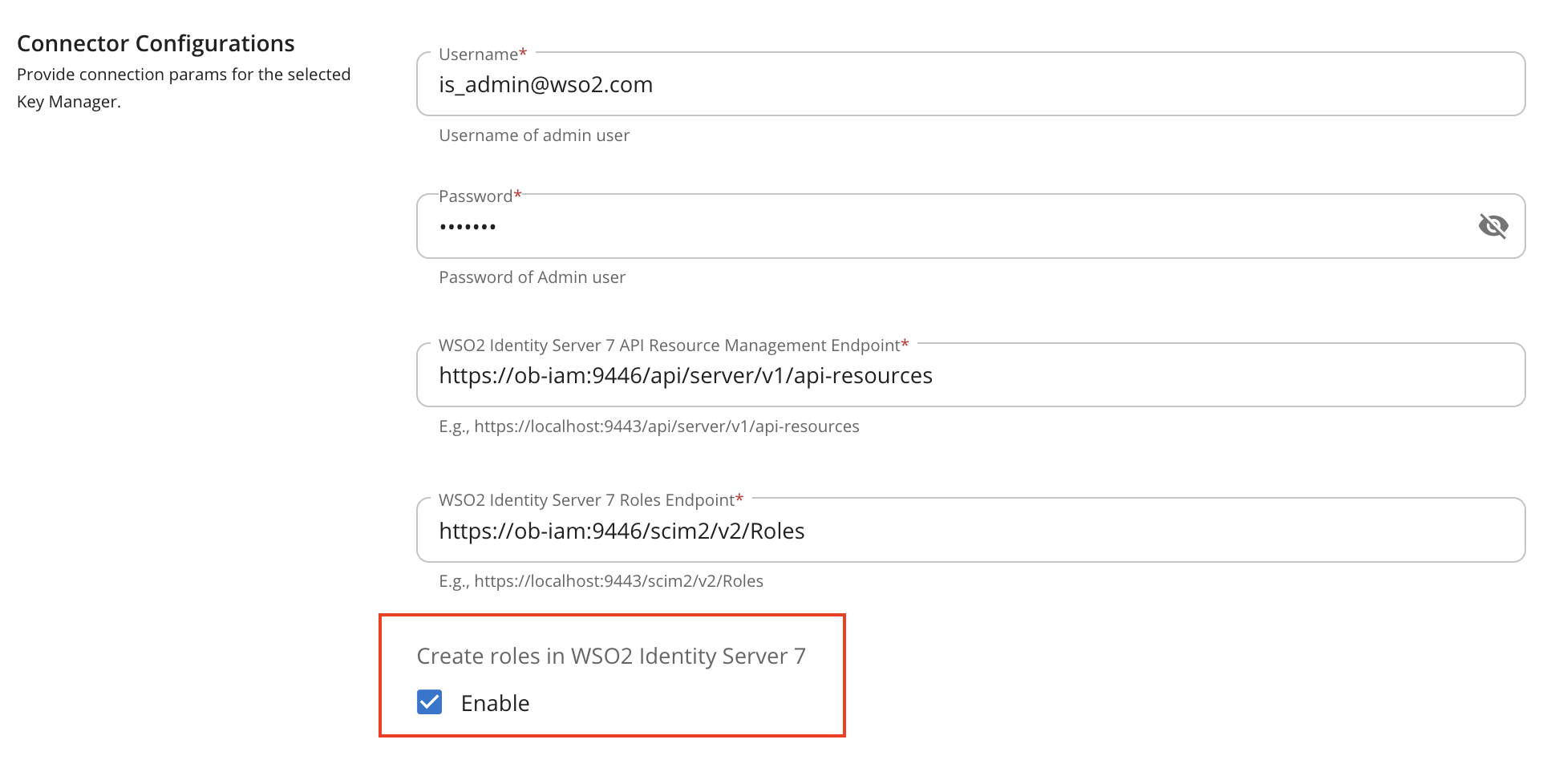
-
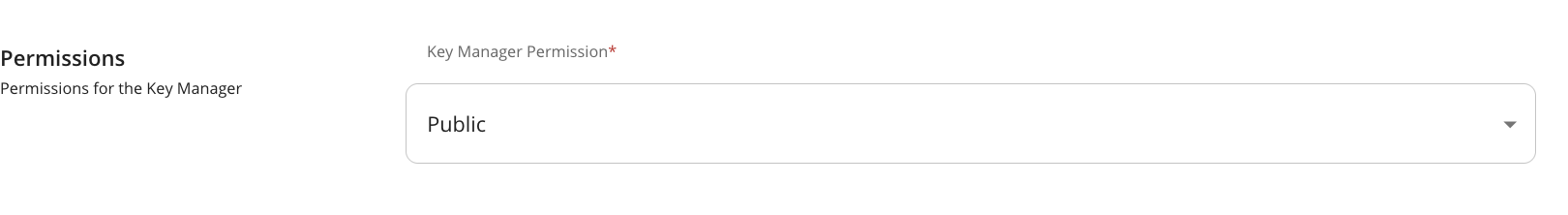
Set Key Manager Permission to Public.
-
Under Advanced Configuration, provide the following values:
Configuration Values Token Generation Tick (Mandatory) Out Of Band Provisioning Tick (Mandatory) Oauth App Creation Tick (Mandatory) Token Validation Method Self Validate JWT Token Handling Options (Optional) JWT -
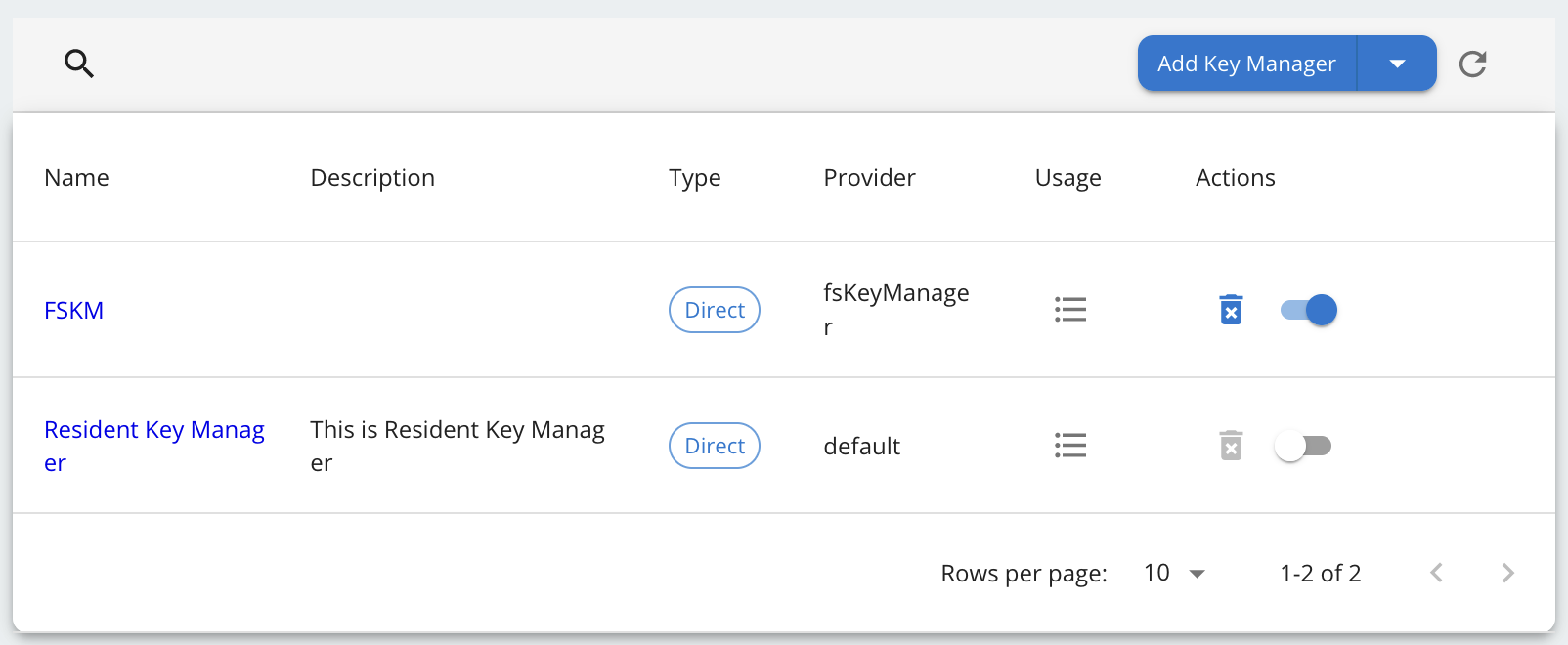
Click on Add button to create the Key Manager. Key Manager will be displayed as below.
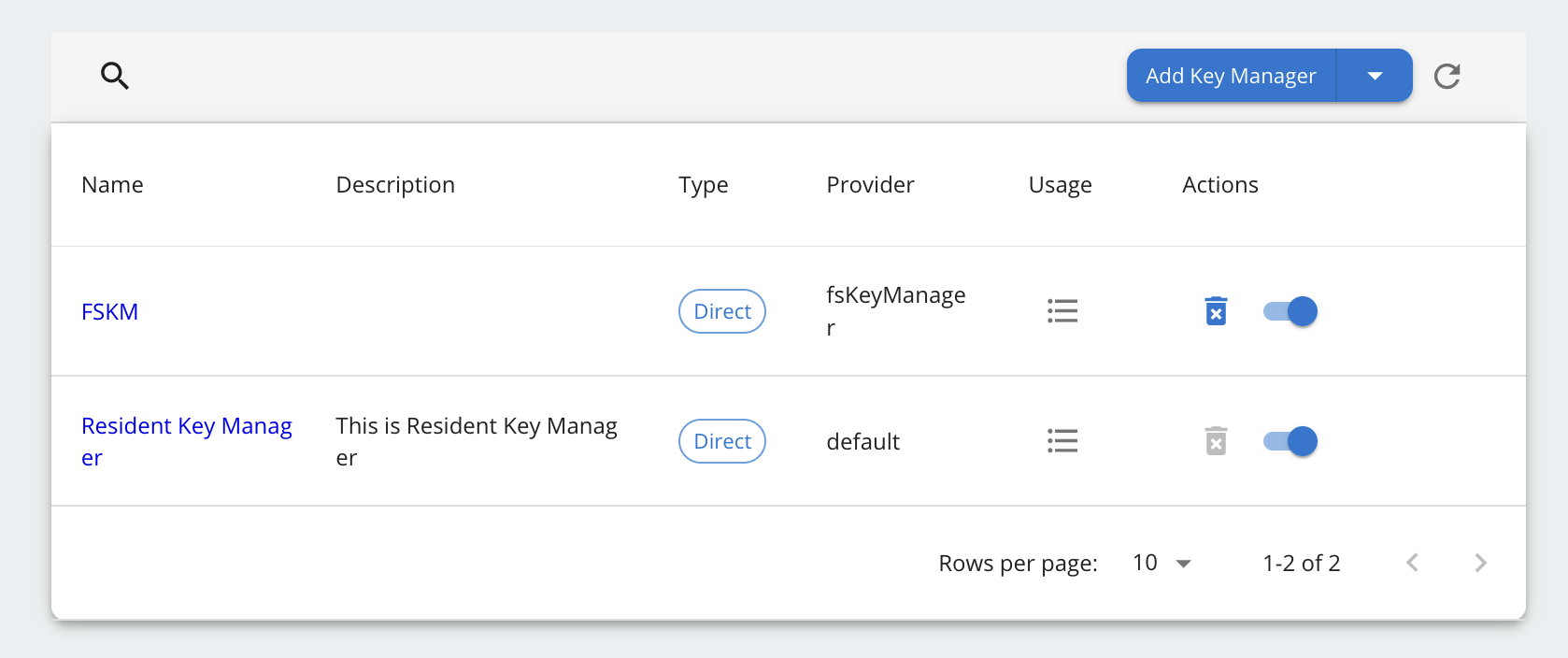
-
Disable the Resident Key Manager.
Create Application using Manual Client Registration¶
Step 1: Sign up as a TPP¶
-
Go to the Developer portal at
https://<APIM_HOST>:9443/devportal. -
Go to the Applications tab.

-
In the Sign-in form, click Create Account.
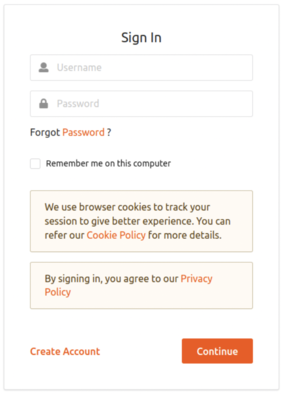
-
Provide a username and click Proceed Self Register.

-
Fill out the Create New Account form to complete registration.
-
Read terms and conditions and click the checkbox to agree to the terms and conditions.

-
Click Register.
Step 2: Sign in to the Developer Portal as the TPP¶
-
Now, sign in to the Developer portal as the TPP.
-
Enter the username and the password you entered when signing up as a TPP.
-
Click Continue. Now, you are on the home page of the Developer Portal.
Step 3: Create an application¶
-
In the Developer Portal, go to the Applications tab.

-
Click ADD NEW APPLICATION. applications_tab
-
Enter the following application details.

-
Click SAVE. The Developer Portal displays the created application as follows:

The application created via the Developer Portal allows you to observe statistics of APIs, subscribe to APIs, and access the subscribed APIs.
Step 4: Subscribe to API¶
-
Go to the APIs tab in the Developer portal.

-
Select the API.

-
Go to Subscriptions at the bottom of the API and select SUBSCRIBE.
-
Select your application from the drop-down list then set the Throttling Policy and click SUBSCRIBE. Once subscribed, the application can access all the supported services of the API resources.
Step 5: Generate keys¶
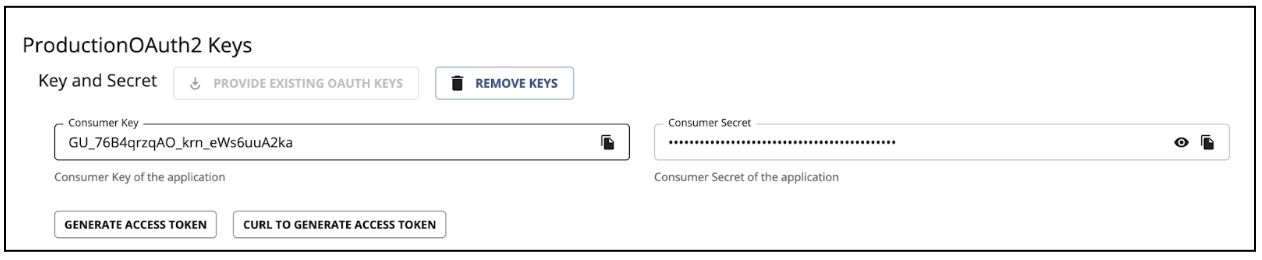
The TPP application requires a Client ID (Consumer Key) to access the subscribed API.
-
Go to the Applications tab in the Developer Portal.
-
From the application list, select your application, which has subscribed to the API.
-
Select Production Keys > OAuth2 Tokens or Sandbox Keys > OAuth2 Tokens according to the type of key you require: a. Production Keys: Generates access tokens in the production environment. b. Sandbox Keys: Generates access tokens in the sandbox environment.

-
Provide the requested information as defined below:
Field Description Grant Types Determine the credentials that are used to generate the access token. - Code: Relates to the authorisation code grant type and is applicable when consuming the API as a user. It is mandatory to select the code grant type for regulatory applications.
- Client Credentials: Relates to the client credentials grant type and is applicable when consuming the API as an application.
- Refresh Token: To renew an expired access token.
Callback URL The URL used by the TPP to receive the authorization code sent from the bank. The authorisation code can be used later to generate an OAuth2 access token.
This is a mandatory field for the authorization code grant type.Enable PKCE Enable if you want to enable PKCE support for your application Support PKCE Plain text Enable if you want to enable PKCE Plain Text support for your application Application Certificate This is the content of the application certificate (.PEM). For Regulatory applications, it is mandatory to use an application certificate Regulatory Application The type of application. If your application complies with the Open Banking Regulation, it is a Regulatory application. 

-
Click GENERATE KEYS to generate production or sandbox keys.
-
It generates the consumer key and consumer secret and displays them at the top of the page.